Assume Your Agency
Has Been Breached
Take action to protect sensitive assets and minimize exposure.
Protect Privileged
Access at All Costs
The December 2020 discovery of the SolarWinds Orion breach has impacted more than 18,000 organizations, including several federal government agencies. Unique in its sophistication, scope, and scale, what the attack had in common with others was its use of compromised privileged credentials. Once the attackers got in, they stole and abused credentials, used the stolen credentials to traverse networks looking for high-value targets, and worked to gain unauthorized access to privileged accounts. They then used those accounts to elevate privileges to steal confidential information. The full impact of this breach could take several months to decipher, but there are steps agencies can take now to mitigate their risks and lessen the damage.

Prioritize What Matters Most to Contain the Damage
Modern IT environments are decentralized, which means ever-expanding enterprise attack surfaces. Attackers are well aware of this, which is why securing privileged access is vital for every agency. In fact, implementing privileged access controls is a Top 5 CIS Critical Security Control and a NIST 800-53 requirement.
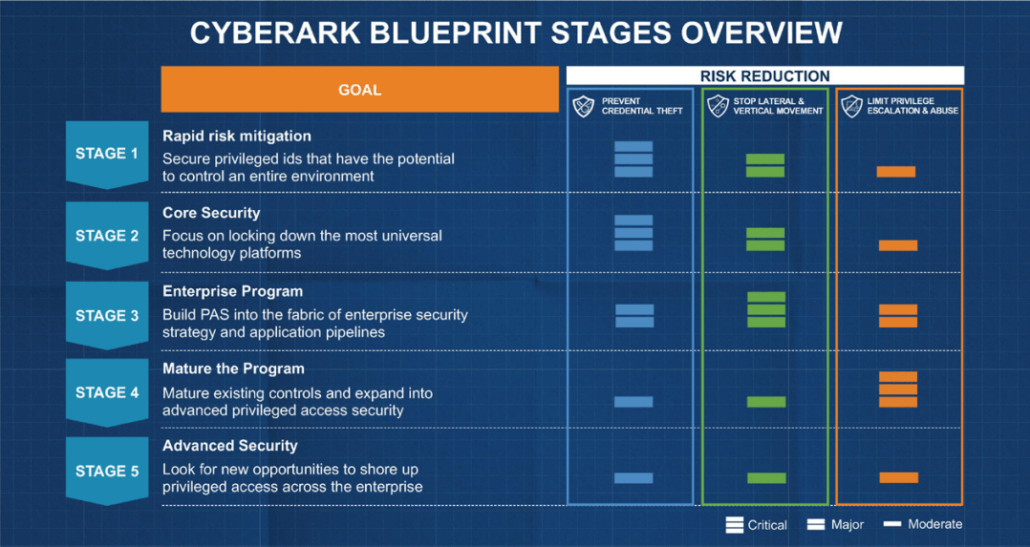
The SolarWinds attack underscores the urgent need for privileged access management (PAM). CyberArk is the global leader in PAM and has the industry’s most complete solution for reducing the risks created by privileged credentials and secrets. Its platform provides deep identity security controls and privileged remediation services that help detect attacks earlier and stop data theft or disruptions before they start.
As a first step, every agency should adopt an “assume breach” mindset that works to contain any damage. By assuming attackers already have access and by thinking like them, agencies can focus their time and effort on protecting the “Crown Jewels.” Agencies can then secure their highest-value assets and prevent any mission disruption by taking these four steps:
- Prioritizing privileged access security
- Deploying a PAM solution, or validating the effectiveness of their existing PAM tool
- Rotating privileged credentials regularly and isolating privileged sessions
- Monitoring and detecting abnormal privileged user behavior
Discover How CyberArk Can Help
CyberArk is the market leader and trusted expert in PAM for the federal government. Its comprehensive platform manages and secures service accounts, whether they’re local or domain accounts. CyberArk’s Core Privileged Access Security Solution centrally secures and controls access to privileged credentials, isolates and monitors admin sessions, and detects, alerts, and responds to anomalous privileged activity.
In the SolarWinds Orion breach, the malware performed abnormal activities, created new user accounts, and accessed other devices. CyberArk could have immediately shut down new accounts and brought attention to the rogue behavior. Learn how by requesting a demo of this powerful solution.





